Download and Convert YouTube Videos to MP3 with Metadata
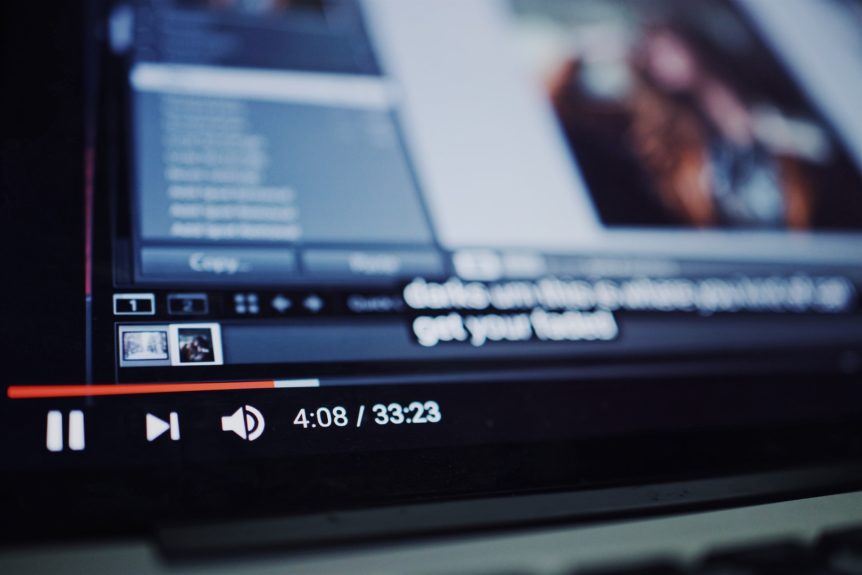
youtube-dl is a great tool for downloading YouTube playlists, videos or music. The tool runs on all platforms, Windows, Linux and Mac. The tool provides many options, for more details check the README file of youbube-dl. Sometimes I like to listen to songs while being able to read their lyrics without googling them individually. In this post, I explain how ...